Restricting virtual machines in VMware Workstation
Many times, especially in a development environment you need to share your VMs with a partner company or with an external contractor but you don’t want those machines to work like forever or be modified. You will want to put some restrictions on them. Since VMware has done such a great job with their Workstation product, we are able to apply those restrictions and share our VMs with others, knowing we have a bit of control over them.
UPDATE! Starting with VMware Workstation 16 this feature is deprecated.
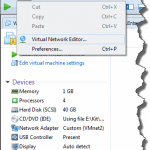
The process is pretty easy and straight forward. All we have to do is open the VM settings by clicking the Edit the virtual machine settings link then go to Options > Access Control.
What we can see right from the start, is that we cannot apply any restrictions to the VM until we encrypt it; so let’s do just that. Click the Encrypt button then provide a password to protect the VM. Make sure you don’t lose the password or you will not be able to use the VM or decrypt it for that matter. Also, this password will need to be shared with the people that need access to the VM(s) in order for them to be able to start it.
Once we click the Encrypt button, the encryption process will start and it might take a long time to complete if you have a large VM or a slow drive.
In case you are using linked clones, be careful that only the linked clone VM will be encrypted leaving the base VM unencrypted. Also, with linked clones it will be very hard to share the VM because you will have to copy the base VM and the linked clone one. For short, try not to use linked clones when implementing VM access control.
Once the encryption progress bar hits 100% the VM will be encrypted, and we can see this in the Summary column of the VM settings.
If we open the .VMX file of the VM, all the content will be scrambled and unreadable. Any change to this file will make the VM unavailable, and we will not be able to start it, so try not to edit the file.
The VM is now ready to be shared with other people, but don’t forget to send the encryption password because it’s needed when importing it in VMware Workstation, VMware Player or Fusion. Once imported, the user can run the VM as he wishes if it doesn’t have any restrictions.
Setting up restrictions on VMs
Restrictions, as the name implies, limit the usage of the VM(s). This are needed from one case to another, but most of the times you will want to put restrictions on VMs because of licensing for a software you are selling or you don’t want the machine settings to be modified. The restrictions that VMware Workstation provides are not a lot, actually they are just a few I can say, but for a few VMs to share here and there are enough. For more you will need to buy the VMware Horizon Felx product which provides centralized control for the VMs you want to restrict and also a lot more restriction policies.
Right now if we open the settings of our VM and check the Enable restrictions box, we can configure all the restrictions VMware Workstation provides us.
- Restrictions password – Yes, another password, but this one is to protect the restriction and VM settings from the users so they can’t modify or re-configure them. After the Restrictions password is defined, most of the VM settings will be grayed-out. The only ones left for the user to modify are the CPU, memory and the network adapter(s). In order to change the settings of a restricted virtual machine you have to click the Unlock All Settings button from the left down corner and provide the Restrictions password.
- Restrictions type – There are tow of them: Fixed and Managed. The first one, and the default one is revealing the default VMware Workstation restrictions while the second one gives us the option to use a Horizon Flex server for improved manageability and restriction policies.
- Require the user to change the encryption password when this virtual machine is moved or copied – By checking this box, every time the user moves or copies the VM to another host it will be asked to change the encryption password. Failing to do so, the VM won’t start.
- Allow USB devices to be connected to this virtual machine – This is self explanatory, but if this box is un-checked, the user will not be able to connect a USB device to the VM and they are presented with the bellow message.
Cannot connect ‘Validity Sensor (VFS471)’ to this virtual machine. The device is not allowed by the virtual machine configuration.
- Expire the virtual machine after: – If enabled, we can set the virtual machine to expire and the user will not be able to power it on. This option also reveals some advanced settings (click the Advanced button) that we can configure, like messages to show to the user(s) when the VM is expired or before it expires.
We also have a time server, and you might ask why. Well…think about it, the user can set the clock backwards on the host system and the machine will not be expired anymore, and every time it expires, he or she just sets the time back with a few days and use the machine for as long as he/she wants. By putting an NTP server in place the VM will get the time from this NTP server and it will not depend on the system/CMOS time.
Summary
Being able to restrict VMs on VMware Workstation is definitely a useful feature especially if you are a developer or tester and need to share those VMs with different people. I guess the biggest advantage of this feature is that you can set the machines to expire. Test it and leave a comment on how it works and in what environment are you using it.
Want content like this delivered right to your
email inbox?

Hello Adrian,
VMware removed the restricted VMs in Version 16:
https://docs.vmware.com/en/VMware-Workstation-Player/16/rn/VMware-Workstation-16-Player-Release-Notes.html#ProductSupportNotices
Are you aware of any alternative for this use case?
Thank you and kind regards
Stefan
Hi,
Thanks for the update, I will put it in the article. Unfortunately I could not find any other solution for this. Maybe some software companies will start releasing something in the future, but that’s just a guess.